
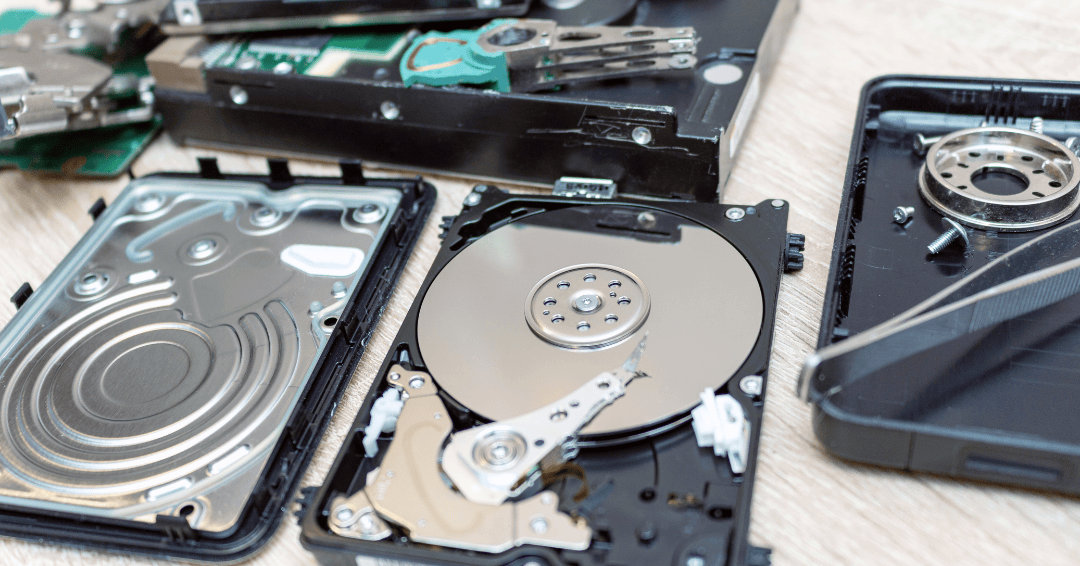
If you’re looking for a secure and reliable way to dispose of your hard drives, solid-state drives,...

If you’re looking for a secure and reliable way to dispose of your hard drives, solid-state drives,...
With the digital age comes the necessity to store, manage and protect sensitive information. From...

Technology is at the forefront of nearly every company's operations. It's critical to success,...

In 2023, the average cost of a data breach soared to a record US$4.45 million, as reported by IBM...

Every business works with data stored on tapes, hard disks and other electronic media devices. In...
The IBM Security Cost Of A Data Breach Report 2020 states that the global average cost of a data...

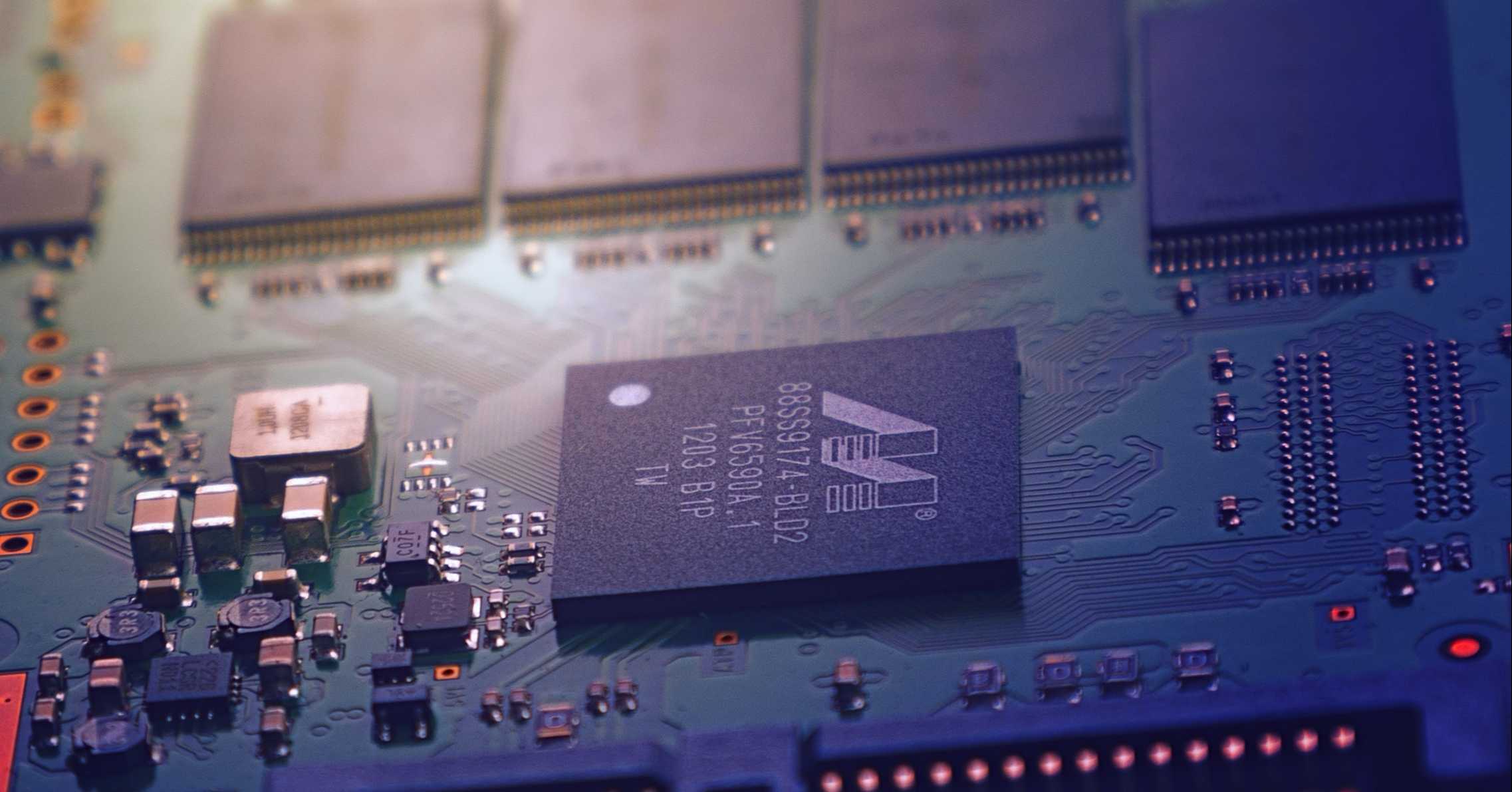
Despite SSDs becoming mainstream, many businesses are still using dated approaches to destroying...

IT Asset and Data Centre Management is an incredibly busy and challenging function, however,...

IT professionals highlight concerns on potential data breaches, compliance penalties, and...